Zero Trust
Infrastructure Intelligence
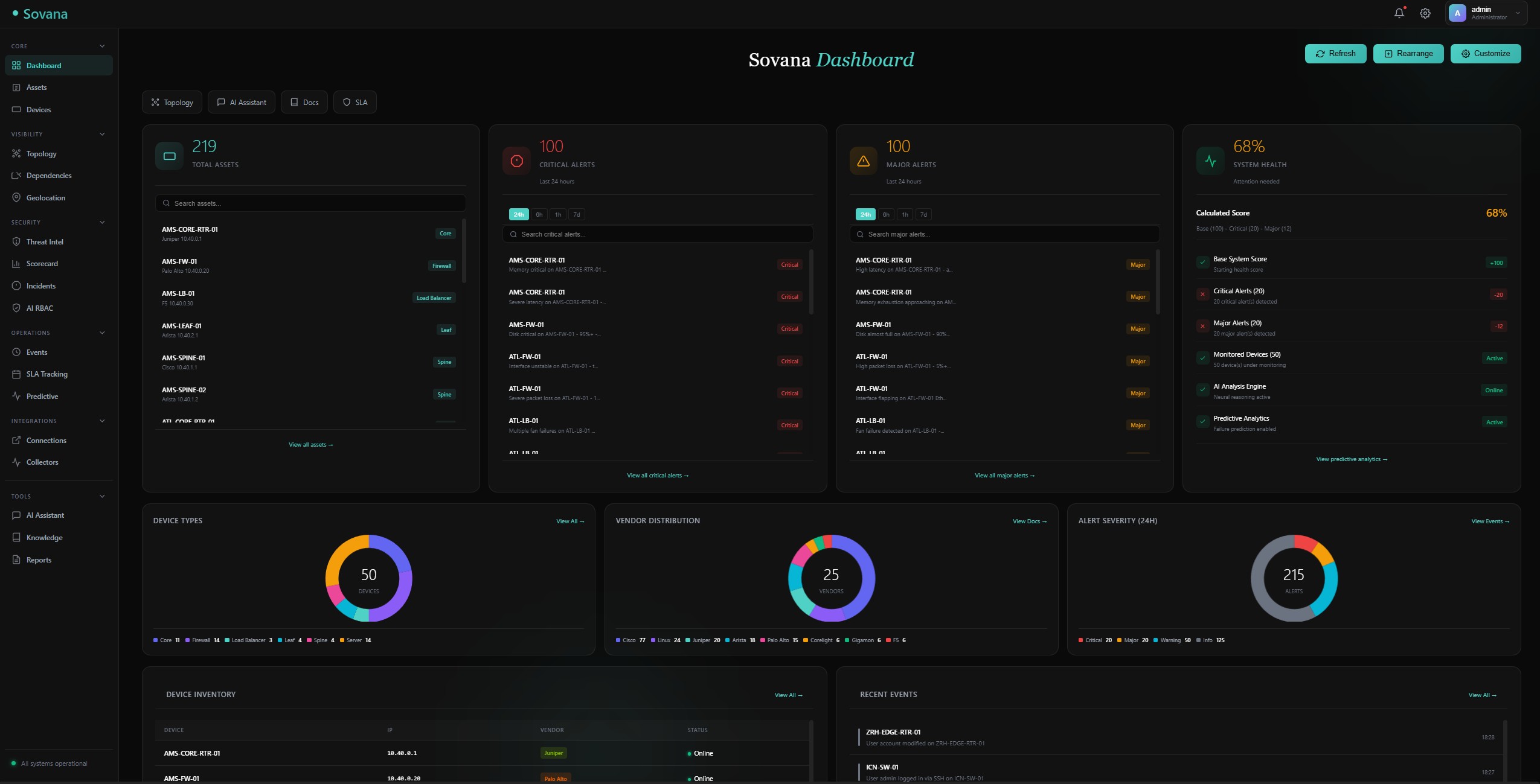
The gap between monitoring and security is where outages happen.
Your NOC tools show you what's happening. Your security tools protect the perimeter. But who's watching for the config drift that will cause tomorrow's outage? Who's validating that credentials aren't hardcoded? Who's correlating datacenter temperatures with device failures?
Sovana closes the gap. Predict. Validate. Remediate. Audit everything.
Veteran-Owned Business
The Gap in Infrastructure Operations
Every tool does one thing. Nobody sees the whole picture.
Monitoring Tools
Show you metrics and alerts. But they don't predict failures, validate configs, or tell you why something happened.
"Interface is down" - but why? And could we have prevented it?
Security Tools
Protect the perimeter, scan for vulnerabilities. But they don't understand infrastructure operations or correlate device health with security posture.
"Credential found in config" - but which devices? What's the blast radius?
Automation Tools
Execute playbooks. But they run blind without validation, without understanding impact, without predicting consequences.
"Config pushed successfully" - but did it break anything downstream?
Sovana bridges all three. Unified intelligence with Zero Trust principles.
The Uncomfortable Truth
Your Zero Trust Architecture Runs on Implicit Trust
Every Zero Trust framework says: "Assume the network is hostile. Never trust, always verify."
So you deploy Zscaler. Okta. CrowdStrike. Palo Alto Prisma. You verify every user, every device, every session.
But here's what nobody asks: Who verifies the network itself?
Your Zero Trust Policy
- Users must authenticate with MFA
- Devices must pass posture checks
- Sessions are continuously validated
- Least privilege enforced everywhere
Your Network Infrastructure
- Engineers SSH with shared credentials
- No posture check on the router itself
- Config changes aren't validated against policy
- Admin access = god mode, no least privilege
The Scenario That Should Terrify You
An attacker compromises a network engineer's laptop. Now they have:
- SSH access to core infrastructure
- The ability to add
permit ip any anyto your firewall - The ability to redirect traffic wherever they want
- The ability to add backdoor user accounts
Your $10M Zero Trust stack doesn't see it. Because it trusts the network.
SIEM sees an SSH session (legitimate user, legitimate source). No diff of what config changed. No validation that the change was authorized. No alert that an ACL went from 50 rules to 51.
"You don't have Zero Trust. You have Zero Trust for users and implicit trust for infrastructure."
Sovana closes that gap.
Zero Trust for Infrastructure Operations
Not just network zero trust. Operational zero trust. Verify everything. Audit everything.
Secure Credential Vault
Every credential encrypted at rest with Fernet encryption. Automatic rotation policies (30/60/90 days). Full audit trail of every access. No more passwords in configs, scripts, or spreadsheets.
- AES-256 encryption with unique master keys
- Automatic expiration alerts
- Access logging with IP and user tracking
- Role-based credential access
Config Validation Engine
Continuous validation across all devices. Detect missing NTP, unsecured SNMP, default credentials, routing inconsistencies. Health scores per device, per datacenter, per network.
- Multi-vendor config parsing (Cisco, Juniper, Arista, Palo Alto)
- Compliance rule library (NIST, CIS, custom)
- Dependency mapping across devices
- One-click remediation with audit trails
Complete Audit Logging
Every action logged. Every credential access tracked. Every config change recorded. Every remediation documented. Immutable audit trails for compliance and forensics.
- SIEM-ready log export
- Tamper-proof audit storage
- User activity timeline
- Compliance report generation
Verified Remediation
Never trust, always verify. Every auto-remediation validates before and after. Rollback capability for every change. Approval workflows for high-impact actions.
- Pre-execution impact analysis
- Post-execution verification
- Automatic rollback on failure
- Multi-tier approval workflows
Deep Config Observability
Finally understand why things break across your multi-vendor environment
Cross-Vendor Config Intelligence
"Why isn't this route working?" Finally get the answer - even when the path crosses Cisco, Juniper, and Arista devices.
Sovana parses and understands configs from 50+ vendors. It maps BGP neighbors, OSPF adjacencies, static routes, ACLs, and NAT rules across your entire environment. When something breaks, Sovana traces the path and tells you exactly where the problem is - even if it's a mismatch between a Cisco ASA and a Palo Alto firewall.
Sovana traces: NYC-CORE-01 (Cisco) → NYC-FW-01 (Palo Alto) → NYC-DIST-02 (Arista)
Found: Missing permit rule on NYC-FW-01 zone policy
Dependency Mapping
See how every device connects to every other device. Understand blast radius before you make changes.
Sovana automatically builds a dependency map from your configs. It knows which devices peer with which, which routes depend on which next-hops, which ACLs reference which objects. Before you change anything, see exactly what will be affected.
- BGP neighbor relationships across vendors
- OSPF area consistency validation
- Static route next-hop reachability
- ACL/firewall rule impact analysis
- VLAN/VRF consistency checking
Config Diff Analysis
See exactly what changed between any two points in time. Correlate config changes with incidents. Know who changed what and when.
Compliance Validation
Continuously validate against NIST, CIS, or custom rules. Detect missing NTP, insecure SNMP, default credentials, and routing inconsistencies in real-time.
Health Scoring
Every device gets a health score based on config validation. Roll up to datacenter scores. Identify your weakest links before they cause outages.
Intelligence That Actually Works
Not dashboards. Not alerts. Actionable intelligence with context.
Predictive Failure Analytics
Detect interface degradation, BGP instability, memory exhaustion, and capacity issues days before outages. Confidence scores, timelines, and recommended actions.
Datacenter Health Correlation
Correlate device health with datacenter conditions. Track issues by location. Identify patterns across facilities. Environmental trends meet device telemetry.
Cross-Vendor Queries
Ask questions in plain English. "Show me all BGP sessions that flapped in the last hour." Get answers that span all vendors with remediation commands.
Self-Healing Automation
Define playbooks that execute with approval workflows. BGP flapping? Memory exhaustion? Sovana detects, proposes, and remediates with full audit trails.
Risk Scoring
Unified risk scores across devices, datacenters, and your entire infrastructure. Know where to focus. Prioritize by impact, not just severity.
Data Retention & Purge
Configurable retention policies per data type. Scheduled purging with preview. Compliance-ready data lifecycle management.
How Sovana Works
Distributed architecture. Collect anywhere. Analyze centrally. Act with verification.
1. Collect
- Distributed collectors at edge
- Syslog, SNMP, gNMI streaming
- Config backup & versioning
- 50+ vendor integrations
2. Validate
- Parse configs across vendors
- Check against compliance rules
- Detect drift from baseline
- Score health per device
3. Predict
- Baseline anomaly detection
- Failure prediction models
- Capacity trend analysis
- Environmental correlation
4. Act
- Verified remediation
- Approval workflows
- Automatic rollback
- Complete audit trail
Built for Enterprise Scale
Real-time intelligence across your entire infrastructure
50M+
Telemetry points daily
50+
Vendor integrations
100%
Audit coverage
0
Hardcoded credentials
Built for Teams Who Can't Afford Gaps
Critical infrastructure requires unified intelligence
Network Operations Centers
Stop firefighting. Start predicting. Correlate events across your entire stack. Get root cause in seconds. Remediate with confidence.
Government & Federal
FedRAMP-ready. Air-gap capable. FISMA compliant. Zero Trust architecture. Built for agencies that need both intelligence and security clearance-ready infrastructure.
Critical Infrastructure
Healthcare, finance, utilities. When downtime isn't an option and compliance isn't optional. Predict failures. Validate continuously. Document everything.
Close the Gap in Your Infrastructure Operations
See how Sovana unifies monitoring, security, and automation with Zero Trust principles.
Request a Demo